If you’re outsourcing customer support for your SaaS business, complying with the California Consumer Privacy Act (CCPA) is non-negotiable. Here’s what you need to know:
- CCPA Basics: The law gives California residents control over their personal data, including rights to know, delete, correct, and opt out of data sharing or sales.
- Your Responsibility: Even when outsourcing, you’re accountable for how vendors handle customer data. Non-compliance can lead to fines up to $7,500 per violation and lawsuits from affected users.
- Key Vendor Requirements:
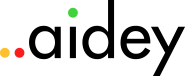
- Vendors must honor six core consumer rights: Limit, Opt-out, Correct, Know, Equal Treatment, and Delete.
- Written contracts must define specific data use purposes and prohibit selling or sharing information.
- Vendors need robust security measures like encryption, access controls, and regular audits.
- New Regulations: Starting January 2026, stricter rules apply, including mandatory audits for automated decision-making technologies.
Bottom Line: Protect your business by using a customer support outsourcing checklist to select vendors with strong privacy practices, clear contracts, and regular compliance monitoring. Neglecting this can cost you millions in fines and reputational damage.
CCPA Compliance Checklist for SaaS Outsourcing Vendors
CCPA Requirements for Outsourced Support
Consumer Rights Under CCPA
Your outsourcing vendor must honor the six "LOCKED" consumer rights: Limit, Opt-out, Correct, Know, Equal Treatment, and Delete. Here’s a quick breakdown:
- Limit: Restrict the use of sensitive personal data, like Social Security numbers or precise geolocation.
- Opt-out: Allow consumers to opt out of data sales or sharing for behavioral advertising.
- Correct: Fix any inaccuracies in personal information.
- Know: Inform consumers about the data collected and its recipients.
- Equal Treatment: Ensure consumers exercising their privacy rights aren’t treated unfairly.
- Delete: Erase personal information upon request.
Your vendor must assist you in addressing these rights within strict timelines. For example, they must confirm receipt of a request within 10 business days, provide a detailed response within 45 calendar days (extendable to 90 days with proper notice), and handle opt-out or limit requests within 15 business days. If a consumer directly approaches your vendor with a request, the vendor must either act according to your guidance or redirect the consumer to your company.
In addition to these rights, your contract must clearly outline your vendor’s CCPA responsibilities.
Service Provider Obligations
Under CCPA, your outsourcing vendor qualifies as a "service provider" only if there’s a written contract with specific language. Without this, any shared data could be considered a sale to a third party, which introduces opt-out requirements and potential penalties.
The contract must clearly define specific business purposes for processing data. Vague terms like "performing the contract" don’t meet CCPA standards. Instead, the agreement must explicitly outline the exact purposes for which data will be used. California regulations emphasize:
A service provider or contractor shall not retain, use, or disclose personal information collected pursuant to its written contract with the business except for the specific business purpose(s) set forth in the written contract.
Additionally, the contract must include strict prohibitions. Your vendor cannot sell or share personal information or use it for their own commercial activities. If the vendor employs subcontractors, those subcontractors must also adhere to the same CCPA-compliant terms. Vendors are required to notify you immediately if they determine they can no longer meet their CCPA obligations, enabling you to take corrective action.
Here are key contractual provisions to ensure compliance:
| Required Contractual Provision | Description |
|---|---|
| No Sale/Sharing | Prohibits selling or sharing personal information. |
| Purpose Limitation | Restricts data use to the specific purposes outlined in the agreement. |
| Audit Rights | Grants you the right to conduct audits or assessments at least once a year. |
| Compliance Notification | Obligates the vendor to inform you if they can’t meet CCPA requirements. |
| Subcontractor Compliance | Ensures subcontractors are bound by identical CCPA-compliant terms. |
sbb-itb-8132e49
Vendor Data Handling and Security Checklist
Encryption and Access Control
Vendors handling personal data must encrypt it both at rest and in transit. This is a fundamental requirement under the CCPA. If a vendor neglects proper security measures and unencrypted data is exposed, consumers have the right to pursue legal action, as previously mentioned.
To further safeguard personal data, enforce a least privilege access model. This includes implementing phishing-resistant multi-factor authentication (MFA) and requiring unique passwords with a minimum of eight characters. For elevated access, Privileged Access Management (PAM) should be used. Additionally, sensitive information, such as Social Security numbers, should be automatically obscured using data masking techniques.
| Security Component | CCPA Regulatory Requirement/Standard |
|---|---|
| Encryption | Applies to data "at rest" and "in transit" |
| Authentication | Phishing-resistant MFA; passwords of at least 8 characters |
| Access Control | Enforce least privilege; use PAM for elevated privileges |
| Data Disposal | Must ensure shredding, erasing, or rendering data unreadable |
| Monitoring | Use IDS/IPS and data-loss-prevention (DLP) systems |
| Audit Frequency | Conduct technical and operational testing annually |
These practices are essential for secure data management and set the stage for effective retention and deletion policies.
Data Retention and Deletion Policies
Vendors should establish clear policies for retaining and disposing of personal data. Once data is no longer needed, it must be securely destroyed – whether by shredding physical documents, erasing digital files, or altering data to make it unreadable.
If a consumer requests data deletion, the vendor must provide documentation confirming the removal or cessation of data use. Keeping proof of deletion not only ensures compliance with the CCPA but also demonstrates your commitment to accountability. These retention and deletion policies should work in tandem with a well-prepared incident response plan.
Incident Response and Breach Notification
Every vendor must have a written incident response plan detailing how they will detect, respond to, and recover from security incidents. This plan should align with the obligations outlined in your vendor agreement. Proper alignment starts during onboarding outsourced customer support to ensure all security protocols are established from day one. The contract must also require vendors to notify you immediately if they can no longer meet their CCPA obligations.
You should retain the right to take action to halt and remediate any unauthorized use of personal data. To ensure ongoing security, vendors should perform regular vulnerability scans and penetration tests, alongside the annual technical and operational testing mentioned earlier. These proactive measures are crucial for maintaining a strong defense against potential breaches.
Vendor Certifications and Agreements
Compliance Certifications
Before committing to any vendor, always request a SOC 2 Type 2 report. This report serves as concrete evidence of a vendor’s security measures – like encryption and access management – being effectively implemented over time. Don’t settle for self-assessments; only a SOC 2 Type 2 report can verify that proper controls are in place.
The California Attorney General mandates that vendors adopt the 20 controls outlined by the Center for Internet Security (CIS) Critical Security Controls. As Omer Imran Malik, Data Privacy Legal Manager at Securiti, puts it:
An organization’s failure to implement all of the [CIS] controls constitutes a lack of reasonable security.
This requirement shapes the definition of "reasonable security" under the CCPA.
For vendors managing high-risk data, insist on annual cybersecurity audits. Your Data Processing Agreement (DPA) should grant you the right to either conduct audits yourself or receive third-party audit results at least once a year. If international data transfers are involved, confirm that U.S.-based vendors participate in the EU-U.S. Data Privacy Framework by checking the official list. These certifications and audits are critical for ensuring compliance with CCPA standards and safeguarding sensitive data.
Data Processing Agreement Requirements
Certifications alone aren’t enough – your DPA must include strict contractual terms. At a minimum, your agreement should prohibit vendors from:
- Selling or sharing personal information.
- Retaining or using data for purposes outside your specified business needs.
- Using data for activities unrelated to your business relationship.
Avoid vague language in your DPA. Instead, define data processing activities with precision – general references like "the entire contract" won’t cut it.
Reasonable and appropriate steps may include ongoing manual reviews and automated scans of the service provider’s system and regular internal or third-party assessments, audits, or other technical and operational testing at least once every 12 months.
Your contract should also give you the authority to stop and address any unauthorized use of personal data. This responsibility extends to subcontractors: your vendor must ensure that any fourth-party providers adhere to the same CCPA requirements. Additionally, if your vendor qualifies as a "contractor" instead of a "service provider", they must provide written certification affirming their understanding and compliance with all restrictions.
The risks are substantial. Civil penalties can reach $7,500 per intentional violation, and if a breach impacts 10,000 individuals due to weak security, damages could exceed $1,000,000. Combining strong contractual protections with reliable certifications is essential for a secure and compliant outsourcing strategy for customer support.
Monitoring and Compliance Assessment
Regular Vendor Reviews
Enforcing audit rights in vendor contracts is a critical step to safeguard your business and reduce support costs. The California Privacy Rights Act (CPRA) emphasizes this:
A business that never enforces the terms of the contract nor exercises its rights to audit or test the service provider’s or contractor’s systems might not be able to rely on the defense that it did not have reason to believe that the service provider or contractor intends to use the personal information in violation of the CCPA.
To meet regulatory standards, schedule technical and operational reviews at least once a year. Vendors managing sensitive data or processing information related to children must undergo annual cybersecurity audits. If a vendor earns 50% or more of its revenue from selling or sharing personal data, classify them as "significant risk".
Combine automated tools with manual reviews to identify potential issues. Automated tools can monitor vendor privacy policies and detect breaches in real time, while manual reviews ensure that vendors’ actual practices align with your Data Processing Agreement. Additionally, perform assessments whenever there are major changes to a vendor’s service model or data handling practices.
Don’t overlook fourth-party subcontractors during these reviews, as they can reveal hidden risks. Also, ensure that vendors properly document compliance with consumer deletion requests.
These regular evaluations contribute to building strong documentation practices.
Compliance Documentation
Maintaining thorough records is essential to demonstrate due diligence during investigations. Centralize key documents, such as signed Data Processing Agreements (DPAs), completed due diligence questionnaires, annual audit reports, deletion certificates, and logs of all consumer requests and responses.
If your business processes personal data for 10,000,000 or more consumers annually, you’re required to track and disclose metrics like the number of requests received, accepted, rejected, and the median response time. Document any compliance issues you identify and detail the steps taken to address them.
To streamline this process, use compliance software to automate evidence collection and minimize errors. Automated alerts can also notify you of any changes to vendor privacy policies, ensuring ongoing alignment with CCPA requirements.
Navigating CCPA Compliance with PrivacyOps and Automation
Conclusion
Staying aligned with CCPA regulations requires SaaS vendor relationship management including careful selection, strong contractual safeguards, and ongoing monitoring to protect consumer rights. Outsourcing partners must prioritize secure data practices and maintain transparency in how they handle information. These steps are key to reducing the risks tied to non-compliance.
To keep compliance efforts on track, adopt active management strategies: schedule yearly cybersecurity audits for high-risk processors, closely monitor fourth-party subcontractors, and keep detailed records of all compliance-related activities.
Working with a reliable provider can ease the burden of compliance. Aidey offers round-the-clock customer support outsourcing, free onboarding, system setup, and CCPA-focused training to help ensure consumer rights are respected and California’s documentation requirements are consistently upheld.
FAQs
What CCPA contract terms define a support vendor as a ‘service provider’?
Under the CCPA, a support vendor is considered a service provider if their contract includes specific clauses that align with the law’s requirements. These clauses must:
- Clearly restrict the use of personal data to the agreed-upon purposes.
- Prevent the retention, use, or disclosure of data for any purpose outside the contract’s scope.
- Explicitly forbid selling or sharing personal information.
These contractual terms are crucial for ensuring proper management and lawful use of personal data.
What security controls should my outsourced support team prove they have?
When outsourcing support, it’s crucial to ensure your team prioritizes strong data protection measures that align with the California Consumer Privacy Act (CCPA). Here are some key practices to look for:
- Encryption: Personal data should be encrypted both while stored and during transit to safeguard it from unauthorized access.
- Access Controls: Strict access controls must be in place, ensuring only authorized personnel can handle sensitive information.
- Security Audits: Regular audits help identify and address vulnerabilities, keeping data protection measures up to date.
Beyond technical safeguards, your support team should have well-defined cybersecurity policies, a clear incident response plan, and regular employee training programs to handle potential threats effectively.
Finally, any contractual agreements should clearly outline their security responsibilities. Regularly monitor their practices to ensure compliance and maintain the trust of your customers.
How do I audit and document vendor compliance without slowing support down?
To effectively assess and document vendor compliance, start with a structured third-party risk management checklist. This helps pinpoint critical compliance areas and simplifies the evaluation process. Incorporating automation into documentation and using continuous monitoring tools allows for real-time tracking of compliance while reducing manual work. Make it a habit to update vendor assessments regularly, focusing on factors like contracts and data handling practices. This approach ensures compliance stays on track without interfering with support operations.